I was scheduled to deliver sessions at three Microsoft Ignite The Tour events this spring. All of them have of course been cancelled, but one of the theater sessions I was supposed to deliver was called: "Top 10 need to know: Secure your Teamwork and Productivity tools".
I believe the topic is even more relevant now, after a rush to establish the cloud as an alternative to working with on-premise tools in the classic office. And would like to share my top tips on simple steps to make the productivity space a little more secure for the users and the organization.
It's probably obvious that I can't cover all your needs, or dive into features in detail in just one blog post. Nor am I going through all 10 items I had prepared for the sessions. But hopefully I can give some pointer on what you can look into, or possibly ask your partner for help if needed.
1. Multi factor authentication
The one, most important improvement every organization should implement as soon as possible, is two factor authentication. The most basic set of MFA features is included in every Office 365 suite, and is proven to be very efficient when it comes to securing users from having their accounts "stolen". Even if a user's username and password is stolen, the account can't be logged into without an extra step like a phone call, pin-code or approval through an app. There is no reason why you should not implement this feature today (but inform your users first, or there might be a lot of questions to the help desk when users are prompted to activate it).
Head over to
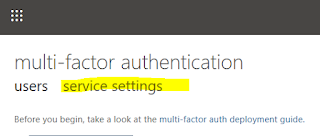
https://admin.microsoft.com and go to the settings section, where you can find the setup of MFA for the organization (Enabling this feature can also be done through conditional access if you have the licenses for it). Many admins neglect to see the "service settings" where you can control types of MFA available for the users, how many days users can "cache" their token on a device and "safe IP Addresses" from where users won't need to use MFA (typically when in the office, or using company vpn)
2. Controlling Sharing and Guest Access
Guest access is a power feature, but without training users can inadvertently add guest into Teams and sites where there shouldn't be guests or where there are sensitive data the company needs to protect. I would encourage everyone to allow Sharing and Guest Access, but not without proper training and control over the sensitive data.
Second, take a look at the guest features in the
Teams Admin Center and disable any of them if you need to (but remember, the idea of having guests in your teams is to engage and collaborate, so don't shut things down just because you can).
You can also take a look at the sharing settings in SharePoint, where you can control global settings for both SharePoint and OneDrive services. At the very least, I recommend the settings shown here, where a guest account and a proper sign-in (and authentication) is required. No anonymous access. If the organization have the capacity or the requirement to do so, I might suggest further lock-down where users can't invite users themselves, but only share with existing guests. This will add to the burden of the IT department, where someone with the proper rights have to add guest users.
3. Control Teams Third Party Usage
By default, Teams allow users to use third party applications and third party storage. While this can be an advantage for many users and organizations who have a strategy to use multiple cloud applications and vendors, this can also be a problem if regulations are required, and protection of certain data is important. I would recommend locking these features down to "Microsoft only" applications and storage, as everything within Microsoft 365 is protected by the features you implement to protect and restrict data. And then you can allow single third party apps where data loss or security breaches are of no concern. Control file storage in the
Teams Admin Center company wide settings, and check out the third party applications in the
apps section.
4. Get to know the security and protection portals
Even though there might not be time right now, to set up everything the way it really should be, take some time to familiar yourself with some of the important security portals in Microsoft 365. Log in, browse the dashboards, and maybe you'll even see some issues and alerts worth looking into. I know that's one strategy to identify the "next step" in securing your environment. Picking the problems as you find them. In an ideal deployment, I would have it the other way around, but I realize a lot of organizations have just been thrown out into the cloud and didn't have the luxury to do so.
Here are some of the portals to pay attention to. And the last one is a gem if you are looking for areas where you may improve on your security today.
Those are my top tips for securing your productivity tools for now. There are a lot more topics I could have covered, or I could have gone into the above topics in more detail. But that would have turned out to be a book, and not a blog post. But if you are interested, here are a few topics you could search for in order to secure your Microsoft 365 Tenant even further. In fact, once the "storm" has calmed down, I highly recommend looking into these areas in depth.
- Conditional Access
- Device Management
- Data Governance
- Threat Protection

