Starting this post with two Exchange Online updates.
Let me begin with a quick user tip: Finding the perfect time for a meeting with participants outside of the company can sometimes be a challenge. I have been using "Find Time" for a long time. But now that add-in is now being replaced by a native scheduling poll feature. Collaboration just got easier!
As many of you probably already know, Microsoft is starting their selective shut down of Basic Authentication on October the 1st (today) 2022. Working with customers I find that many of them have enabled MFA for their users, and these users will not be affected by the change. However, there are a lot of 3.rd party integrations out there, using EWS and other affected services. And these integrations will stop working once basic authentication is shut down.
I wanted to share two easy ways for an organization to figure out if they have such services running or not.
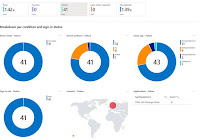
The easy one requires licenses for conditional access, and use of log analytics. Simply create a conditional access rule blocking all legacy authentication, and set it to report only. Within a day or two, you can go to the analytics part of conditional access and see how may "fails" there are. The report will identify any user-id being hit by the report only block.The other method can be performed by filtering the sign-in logs in Azure AD. Head over to the Entra portal (entra.microsoft.com), open "monitoring and health" and select "sign-in logs". Add a filter called "client app", and use the filter to select on all or any of the legacy protocols, "pro tip: I also add a filter for successful logins, failure attempts can also be password spraying"
Comments